What is a security sandbox? Think about the type of sandbox that kids play in. It is small, safe environment where kids can play with just the toys in the sandbox, and they’re temporarily contained so that they can’t touch anything outside the sandbox (unless they leave the sandbox).
In computer security, there is a concept called the principle of least privilege.
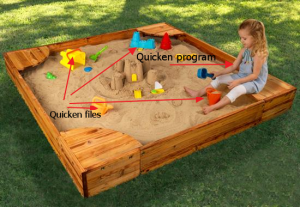
How can we keep our possible malicious programs from accessing our Quicken file? Let me stretch the sandbox analogy a little more. Let’s say that the things in the sandbox are files that our program can access, and let’s say that the little kiddo is our program.
Let’s create two separate security sandboxes. One sandbox will be for Quicken, and the other sandbox will be for our example malicious program.
There are two different sandboxes. The files in one sandbox can only be accessed by the program that runs in that sandbox. If a program runs in a different sandbox, then it can’t see files outside of its own sandbox.
That, in a nutshell, is what a security sandbox is. It is just a “box” that a program can run it, that limits what that program can see and do. It is a way to implement the principle of least privilege.
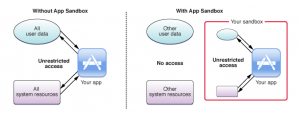
Another way to look at it: The Mac OS X Developer Library has a webpage called About App Sandbox. It’s a pretty helpful diagram:
On the left-hand side, when you run your app without a sandbox, it can access all system resources and all user data on your computer. On the right-hand side, when you run your app in a sandbox, it can only access the resource and user data that it is supposed to access, and no more.
This is great, right? Well, it would be great, except that in Windows 8 and Mac OS X Mountain Lion (10.8) or later, the sandboxes are voluntary. On the right-hand side, you have an app that can only play in their own sandbox. On the left-hand side, you have an app that can play outside the sandboxes, and also inside ALL the sandboxes.
Programs running outside of a sandbox defeat all the security measures that we were trying to put into place by implementing sandboxes in the first place. This is a side-effect of the basic security model of Windows, Mac OS X, and Linux that opens everyone up to security threats.
To learn more about security sandboxes, read:
- All Your Programs Can Access Your Quicken Data
- How to Protect Your Quicken Data from All Your Programs
- Security Sandboxes: A Great Reason to Upgrade
- How to Implement Security Sandboxes
- Security Sandboxes and Virtualization
- Virtual Machines Aren’t Perfect Sandboxes



Recent Comments